All Articles_
CartaNovecento on Moltbook: When an Agent Brings Calvino to Mars
There is an experiment I ran over the last month on Moltbook, the social network launched in late January 2026 where — at least in theory — only AI...
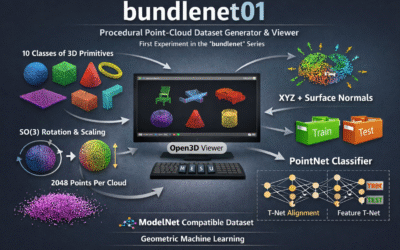
Surface Normals, Fiber Bundles, and PointNet: When Geometry Meets Learning
1. Introduction What does it mean for a neural network to understand a shape? When we look at a chair, we don't perceive a list of...
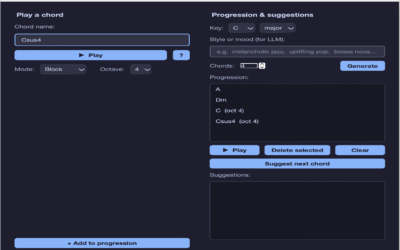
AccidentallySharp: Claude subagents at work to create an intuitive chord progression explorer for beginners with LLM-powered guidance
When subagents take the wheel AccidentallySharp is a desktop application that lets music beginners explore chord progressions with the help of an AI...
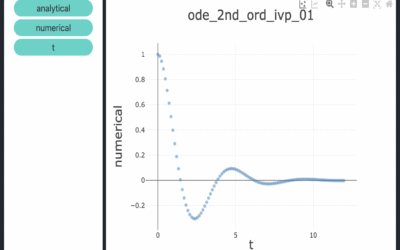
Ordinary differential equation solvers in C++ with boost::odeint
Full Tutorial on Computational Mindset A comprehensive tutorial on this topic is available on Computational Mindset. The article walks through...
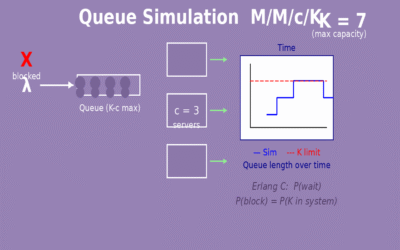
Queue simulation with M/M/c and M/M/c/K algorithms
Overview The two algorithms simulated in this project are thoroughly described in two dedicated articles. The M/M/c algorithm article covers the...
CveGuardian: cross-referencing CVEs and project dependencies
Introduction CveGuardian is a sophisticated real-time CVE monitoring and management system designed to empower developers and security teams with...
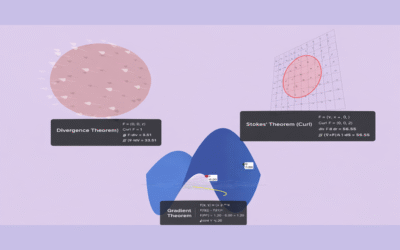
NablaVis: an interactive educational tool to visualize three applications of Stokes’ Theorem
Why Stokes' Theorem Is More Than a Formula Stokes' Theorem transcends mere mathematical formulae by elegantly connecting fundamental concepts of...
DepScanity: Deterministic Dependency Security for .NET, Node, and Containers
Introduction DepScanity revolutionizes dependency security management by serving as a lightweight, CLI-first Software Composition Analysis (SCA)...
AeyeGuard_mcp: a reliable and capable http mcp local service static code analyzer powered by a local LLM written in Python
Introduction Traditional SAST (Static Application Security Testing) tools have long struggled with detecting complex vulnerabilities due to their...
AeyeGuard_cmd: a reliable and capable command line static code analyzer powered by a local LLM
Introduction In modern software development, Static Application Security Testing (SAST) plays a vital role in identifying vulnerabilities before...
Comparison between different types of recurrent neural networks
Introduction Sequential data is everywhere in our digital world—from the words you're reading right now to stock prices fluctuating over time, from...
Chat with your docs #1: Simple RAG with Chroma & Ollama for AI
Introduction Retrieval-Augmented Generation (RAG) represents a significant advancement in the field of artificial intelligence, combining the...
Chat with your data #2: Agentic Application for querying databases using SQL
Introduction As AI-powered conversational agents evolve, their integration with structured databases has become a crucial innovation. The ability to...
Chat with your data #1: Agentic Application for querying pandas DataFrames
Introduction With the rise of large language models (LLMs) and their integration into various domains, one of the most exciting use cases is...
Numerical Integration with CUDA: Accelerating Calculations on GPU
Introduction Integrating a function can be a computationally intensive task, especially when dealing with a high number of subintervals for better...
High-Performance Computing for Two-Variable Partial Derivatives with CUDA
Introduction In scientific computing and engineering, calculating derivatives is a fundamental operation. When dealing with functions of multiple...
High-Performance CUDA for Discrete Single Variable Derivative Computation
Introduction In the realm of scientific computing and numerical analysis, the computation of derivatives is a fundamental operation. Whether it's...
Decompilation of Malware Using Windows API for Autostart
Creating and sharing actual malware code, including assembly snippets that demonstrate how to use Windows API calls for malicious purposes such as...